Design of X.Y Task
Bitstorage auth design
This design has been worked out between Mads (INITIALS), Per (INITALS) and abr. Jhlj has been informed of some of the design, but need to sign of on the final version.
The design is as follows:
Components:
- Doms auth checker: Service for checking credentials against the policy in doms. Author IT Digitale Ressourcer
- IP2RolesMapper: Service for mapping user ip to a set of roles. Auther Unknown.
- URL2FileMapper: Service for mapping a permament url to a file. Authro IT Drift
- PHP main app: Service for handling the flow between the services. Auther IT Service
- Apache server: Server for housing the php app, and handling the perm urls. Use URL_rewrite to forward requests to php.
- Each file in bitstorage is assigned a permanent URL
- An Apache server is set up to handle these URLs
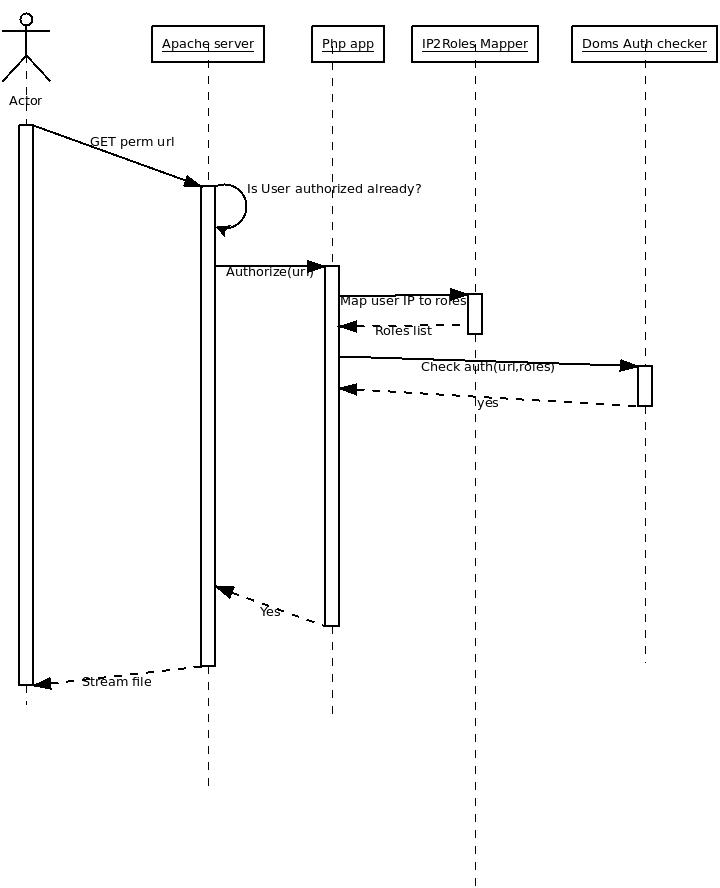
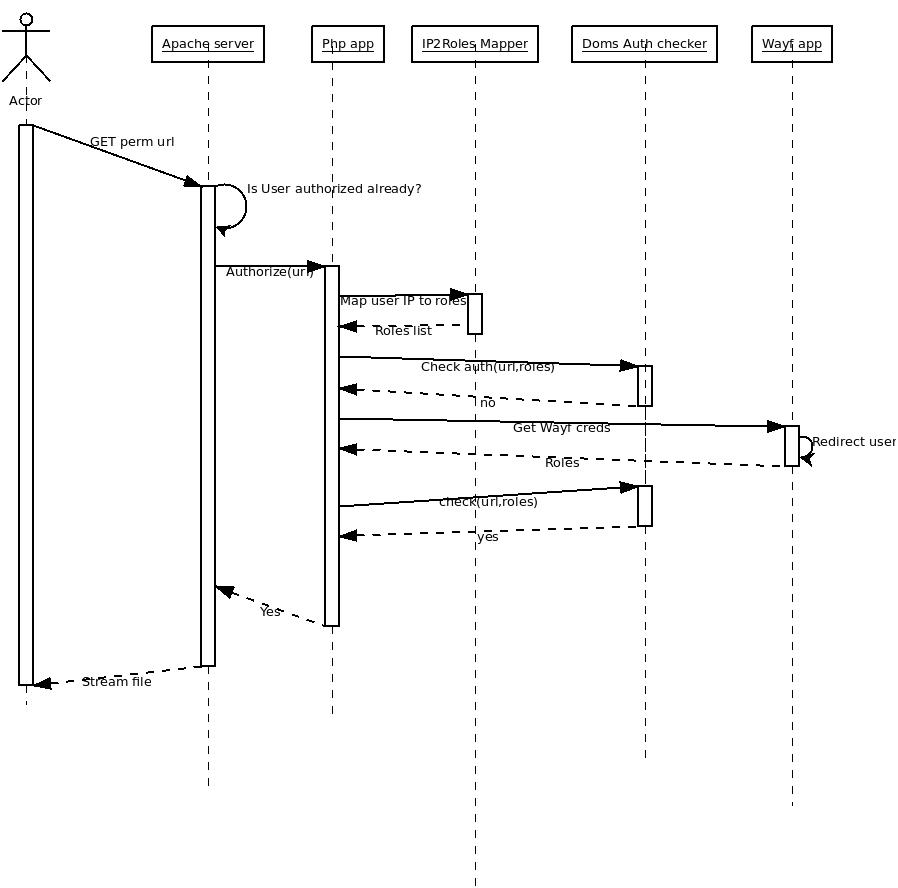
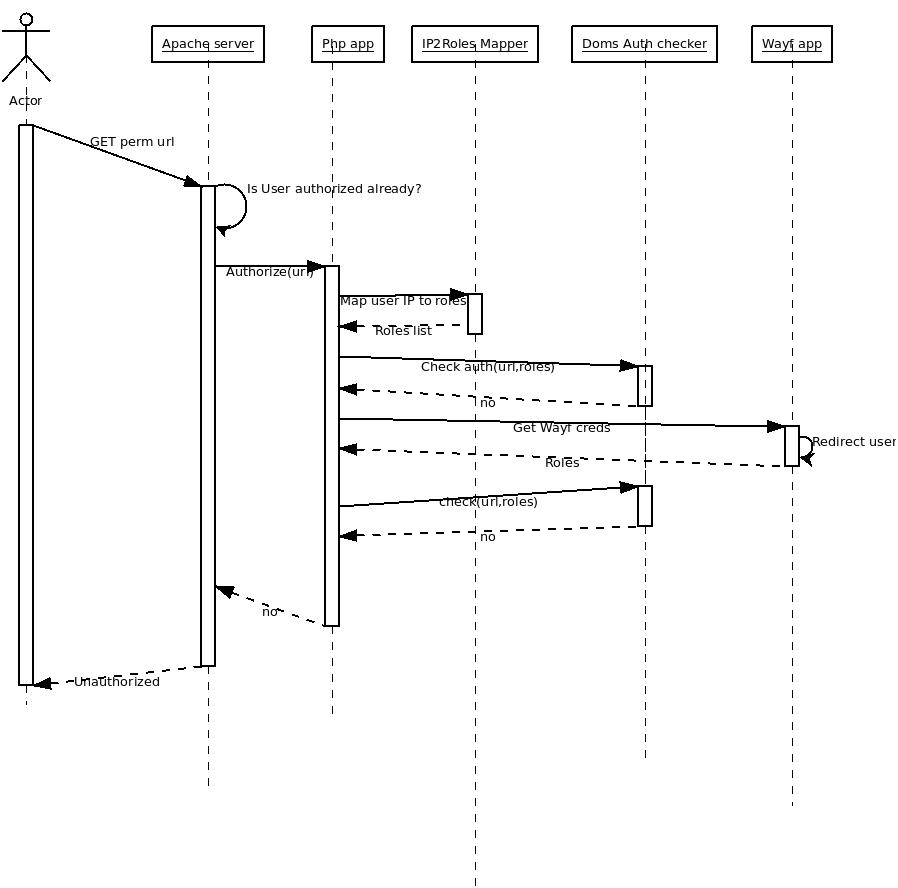
User GETs a perm url
Apache -> url_rewrite the requests and forward it to php app
- Php application
- Invoke IP2RolesMapper to get user roles.
- Invoke Doms Auth Checker(url, roles) to see if the IP roles are enough to get the file
- If no:
- Extract Wayf credentials from the user, by redirecting him to the WAYF page.
- Invoke Doms Auth Checker(url, creds) to see if the file is assesible with the creds
- if no:
- Send Unauthorized error
- Invoke URL2FileMapper to get a file location.
- Open this file.
- (Request file mime-type from Fedora)
- Stream it to the user.
It can be seen that the php app will become a bottleneck. There are several designs that could work around this. Having several identical apache servers with identical php apps, and using some sort of load balancing would work.
IP Roles are enough
Wayf creds needed
No creds good enough
Prerequisites and Design Decisions
Required Software and Modules